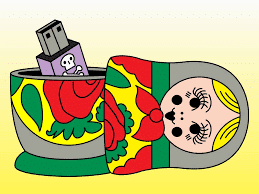
In the event you’re keeping score at home, Russia sits atop the medal standings at the Hacker Olympics. And there’s no indication they’ll lose that top spot any time soon. Unfortunately, these olympics don’t happen every four (4) years. It’s a race that will never end.
In its latest threat report, CrowdStrike, the organization that uncovered Russia’s Democratic National Committee hacking prior to the 2016 election, has determined that Russia is leading the cybercrime pack against nearest competitors North Korea, Chinese and Iran.
It’s a timed event
This Hacker Olympics is comprised of only one (1) event, and it’s measured not with judges or style points, but in time. In this case, it’s called “Breakout time,” a measurement CrowdStrike created that refers to the time between the breach of the initial point of entry (starting line) to the network (finish line). Once the network is reached, the data theft can begin (we’ll call that the medal podium).
According to CrowdStrike, the average breakout time in 2018 was 4 hours and 37 minutes. They garnered these results from analyzing over 30,000 thwarted breach attempts among its customer base. Russia’s gold medal-winning speed? A frightening 18 minutes and 49 seconds.
Here’s how the others fared:
Silver Medal—North Korea (2 hours and 20 minutes)
Bronze Medal—China (4 hours)
Dishonorable Mentions—Iran (5 hours and 9 minutes); Organized criminal groups (9 hours and 42 minutes)
Eight times (8x) faster!
While Russia’s stunningly fast time is impressive—or, rather, scary—what’s probably more concerning is China’s precipitous increase targeting the United States. Russia’s attacks weren’t as prejudiced as China’s and evenly spanned the globe (lucky globe). North Korea’s were highly focused on revenue-generating attacks, and Iran’s were more focused on the Middle East and North African countries, primarily those also in the Gulf Cooperation Council (GCC).
Don’t be a statistic in the Hacker Olympics
To find out how to secure your organization’s network and protect its mission critical data, contact GDT’s tenured and talented engineers and security analysts at SOC@GDT.com. From their Security and Network Operations Centers, they manage, monitor and protect the networks of companies of all sizes, including those for some of the most notable enterprises, service providers, healthcare organizations and government agencies in the world. They’d love to hear from you.